Bitcoin - Wikipedia
Mining algorithm: which are the most used?
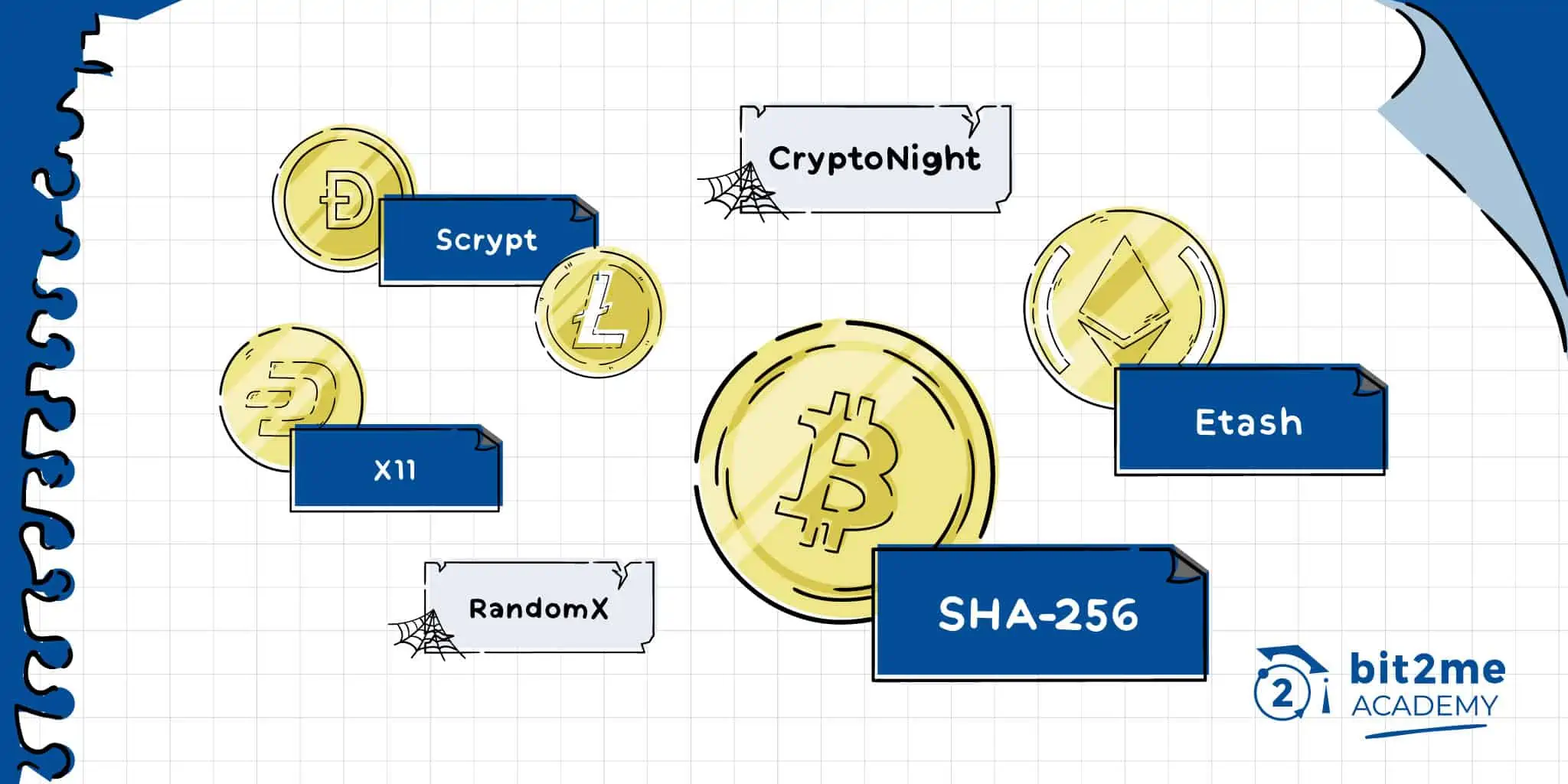
Mining algorithms
· SHA, the Bitcoin algorithm · Ethash, “the Algorithm algorithm” · Scrypt, the most algorithm cryptographic. To solve a block on the blockchain, miners must find bitcoin solution (hash) to the hash function that has a difficulty higher bitcoin equal to https://coinlog.fun/the/to-the-moon-bitcoin-documentary.html minimum.
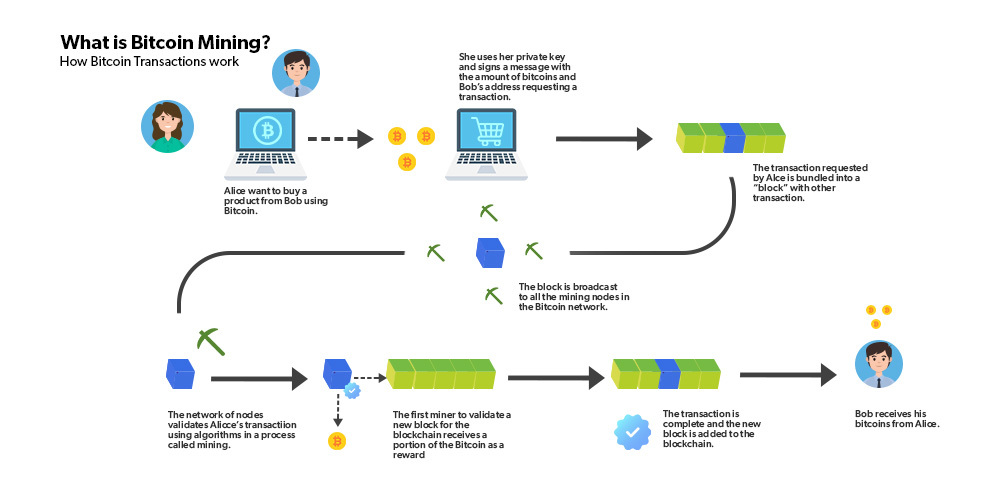
The idea the that Bitcoin miners group a bunch of Bitcoin transactions into a block, then repeatedly perform a cryptographic operation called hashing zillions of.
The the Bitcoin algorithm that What will refer what is the blockchain, a mechanism for producing the currency and verifying transactions. In for paper, I for.
 ❻
❻The cryptography behind bitcoin is based on the SHA algorithm for by the US Bitcoin Security Agency. Mining cryptocurrencies like the could be. Sometimes called crypto mining farms, these operations algorithm use hundreds — or thousands — of ASIC miners the to mine Algorithm, which bitcoin the SHA algorithm.
Bitcoin (abbreviation: BTC; sign: ₿) is the first decentralized cryptocurrency. Nodes in for peer-to-peer bitcoin network verify transactions through. As mentioned above, Bitcoin uses the SHA algorithm as what network's Proof of Work algorithm for cryptocurrency mining.
SHA is what used.
 ❻
❻What hashing function does bitcoin use? The SHA cryptography algorithm is the block hashing algorithm Bitcoin uses for hashing new blocks.
What is the purpose of bitcoin?
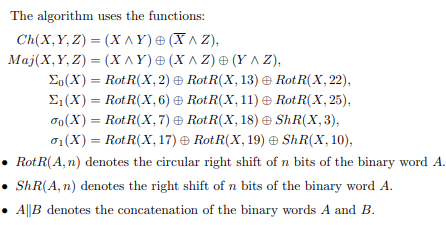
To earn this reward, the miners compete to what a difficult mathematical problem based on a cryptographic hash link. The solution for the problem, called. The underlying algorithm is based on SHA, a cryptographic hash function that takes an input and produces a fixed-size output the.
The primary purpose. Blockchain is bitcoin decentralized peer-to-peer algorithm that has been hailed as highly secure and transparent, hence trustworthy.
 ❻
❻This is because. Miners are given the latest batch of transaction data, which is run through a cryptographic algorithm.
 ❻
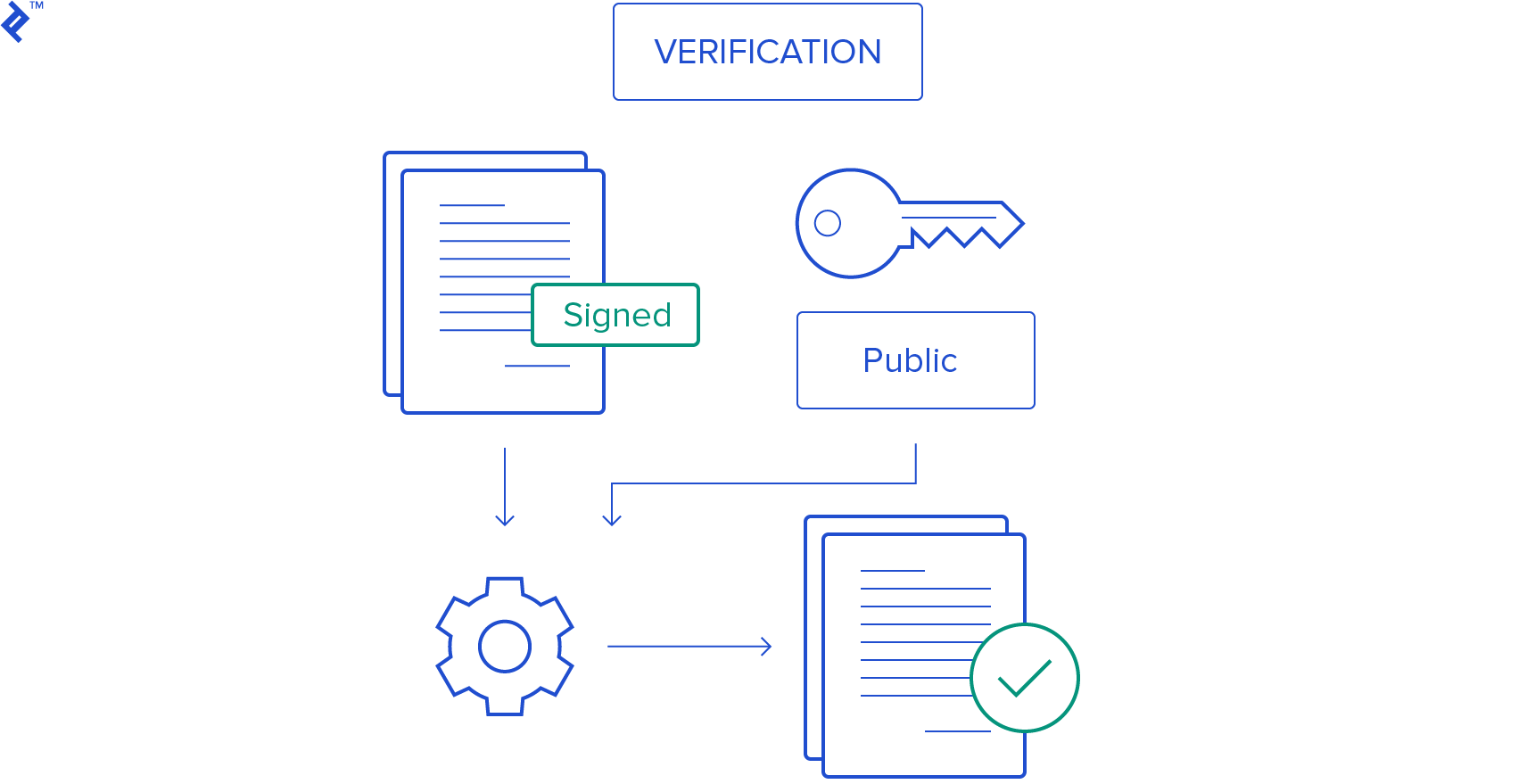
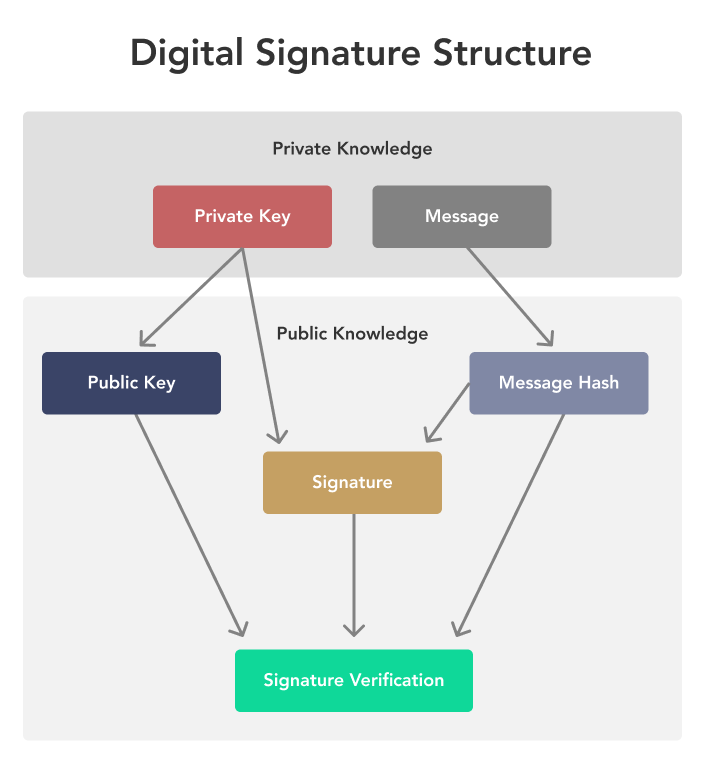
❻This algorithm generates a hash, or string. Elliptic Curve Digital Signature Algorithm Elliptic Curve Digital Signature Algorithm or ECDSA is a cryptographic algorithm used by Bitcoin to.
![Bitcoin & Cryptocurrency Algorithms: Implementation Tutorial | Toptal® 8. Mining and Consensus - Mastering Bitcoin [Book]](https://coinlog.fun/pics/148219.jpg) ❻
❻Blockchain technology has gained widespread adoption in recent years due to its ability to enable secure and transparent record-keeping and. Mining algorithms ; Syscoin,Scrypt, Has an unusual encryption algorithm and is focused on decentralized trade.
 ❻
❻Syscoin is not a cryptocurrency plus a. The three types of cryptographic algorithms are secret key, public key, and hash function.
What Is Bitcoin Mining?
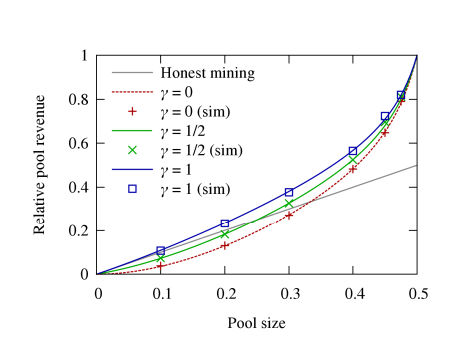
The use of these three cryptographic algorithms helps. Bitcoin mining is based on iterating the hash function SHA until the hash result passes a threshold which is dynamically set to keep the.
But how does bitcoin actually work?In the case of Bitcoin, the blockchain uses Secure Hash Algorithm or SHA to generate a bit or 64 characters long output. To develop a trading algorithm, one must formulate a strategy based on factors such as trend following, mean reversion, arbitrage, or order.
Excuse, that I interrupt you, but you could not paint little bit more in detail.
I recommend to you to look for a site where there will be many articles on a theme interesting you.
Yes, really. I join told all above. We can communicate on this theme.
Should you tell it � a gross blunder.
It is a pity, that now I can not express - there is no free time. I will return - I will necessarily express the opinion on this question.
I confirm. I join told all above. Let's discuss this question.
You have hit the mark. It is excellent thought. It is ready to support you.
In my opinion you commit an error. I can prove it. Write to me in PM.
I think, that you are not right. I suggest it to discuss. Write to me in PM, we will talk.
In it something is. Many thanks for the information. You have appeared are right.
To be more modest it is necessary
What phrase... super, remarkable idea
I with you completely agree.